Artificial intelligence for small businesses: a plain-English guide

Managed IT services give small businesses predictable costs, stronger security, less downtime by replacing reactive break-fix support with proactive management.
Benefits of managed IT services for small businesses

Managed IT services give small businesses predictable costs, stronger security, less downtime by replacing reactive break-fix support with proactive management.
Why outsource IT support? The benefits, risks, and how to choose the right company

Outsource IT support for cost savings, improved security, and expert IT solutions. Find the benefits and risks for your UK business performance and efficiency.
How to choose the best IT support provider for your small business

Learn how to choose the best IT support provider for your small business. Get essential steps, key questions, and practical tips for smooth, secure operations.
How to create a professional email signature that stands out

Get actionable tips and expert insights on creating a professional email signature that enhances branding, builds trust, improves communication, and boosts response rates.
Proactive vs reactive IT support: Why prevention is the key to small business success

Proactive IT support is key to small business success, minimising downtime and boosting productivity. This approach focuses on preventing IT issues before they occur.
Graph vs REST API
You want a quick explanation of the differences between Graph and REST APIs, well you’re in the right place.
PSTN Switch Off and SOGEA Broadband

The withdrawal of legacy PSTN copper phone lines in the UK is underway, and due to complete by 2025. Part of this plan requires moving broadband customers to a new type of connection that we call SOGEA.
Global IT Outage – CrowdStrike users affected

Latest from us on the Global CrowdStrike crash which is affecting millions of computers.
Microsoft 365 Security
Changes This is an important notice to let you know about changes to your Microsoft 365 system which will affect you and your colleagues. Please take the time to read and understand this, and communicate it to your colleagues where necessary. 2FA, or two-factor authentication has been a feature of many systems for several years now, […]
Microsoft 365 Revised Pricing and New Commerce Experience (NCE)

If you weren’t already aware, this is the biggest change to billing that Microsoft have introduced in the history of their 365 product, and the first time they have ever increased the price.
Apache Log4j 2 vulnerability for Dummies
Chances are, if you use any web-based software in the course of your work, you will have heard about something called the “Apache Log4j2” vulnerability, and like most people, you’re probably a bit confused about what it means and what you need to do.
COVID-19 Statement from Openreach

In our capacity as a telecoms provider, Computercentric are heavily reliant on Openreach for support and deployment of telephone line and internet services. Line most businesses during these unpredictable times, Openreach has had to quickly adapt to the changing situation, and this document highlights the disruption and changes which may affect our clients.
Windows 7 – End of the Road

So you’ve left it to the last minute! You know Windows 7 is being retired, but you’ve done nothing about it, and you want to know what your options are, well you’re in the right place.
Cyber Security White Paper for Customers

We’ve produced this white paper as a tool for our customers or visitors to our web site to help you understand and deal with the cyber threats that businesses currently face.
Why is my Office 365 bill so complicated?!
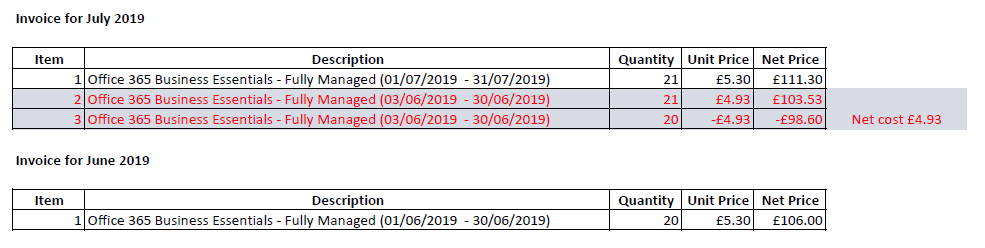
We get this question almost every month, so here is the answer!
Cyber attacks to be aware of!

The increase in cyber-attacks on regular, small / medium sized businesses in the last 18 months has been alarming. Here are the most common attacks we see, and hope you don’t have to.
Windows 7 End of Life Reminder

2020 is fast approaching, make sure you have plans to move away from Windows 7 in time.
Rude parts

An actual sample of data from a bespoke application we’re working on for a client.
Email ‘spoofing’ and why it’s not your fault

Email spoofing, where emails arrive in someone’s mailbox, appearing to have come from you is almost always out of your control, here’s why…
